Preventing Bi-Directional Loops With The State-Hash Guardrail Process
I have observed a recurring pattern among Growth Engineers who are technically proficient enough to build their own integrations but occasionally underestimate the complexity of distributed state management.
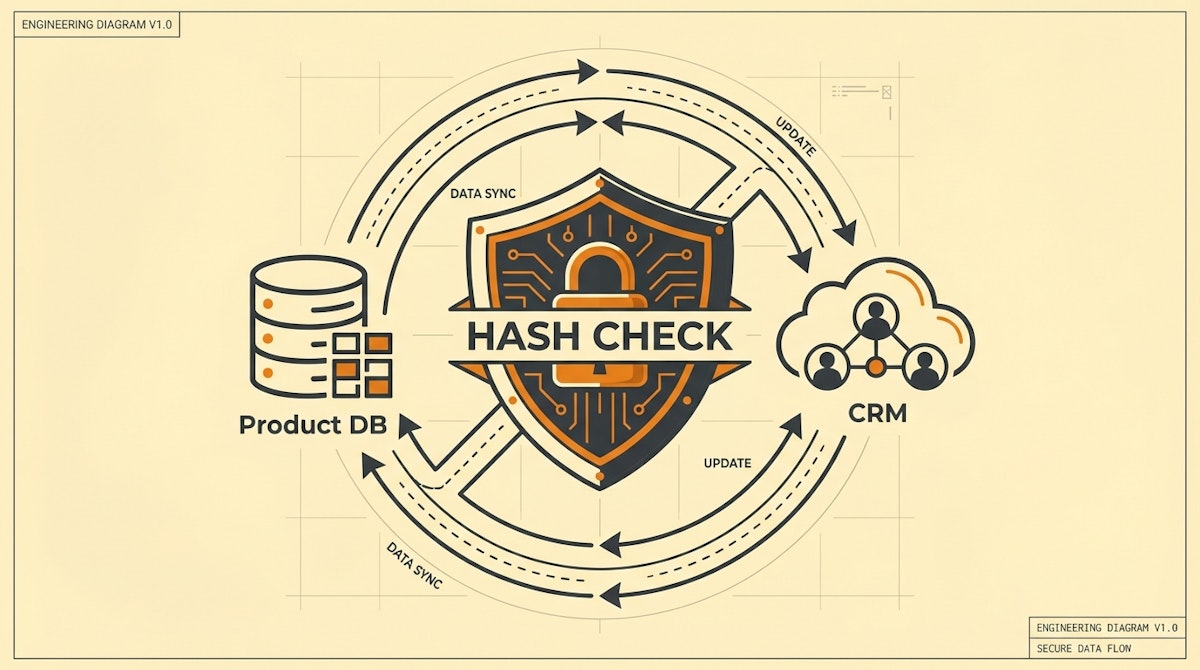
The ambition is usually valid: keeping a Product Database (like PostgreSQL or Firestore) in perfect sync with a CRM (like HubSpot or Salesforce) to trigger personalized marketing journeys based on real-time usage data.
The mistake lies in the architecture of the synchronization logic. Specifically, the "Naive Echo" setup. This happens when you configure an automation to "Watch for Updates" on Platform A to update Platform B, and simultaneously have a separate automation watching Platform B to update Platform A.
Without a strict governance layer, a single field update on the product side updates the CRM, which the CRM detects as a "change," triggering the second workflow to update the product side, and so on.
I have seen this innocent configuration burn through 50,000 operation credits in an hour on platforms like Make or n8n, simply because the automation couldn't distinguish between a meaningful user change and its own echo.
The Engineering Reference: Stripe's Idempotency Keys
To solve this, we can look at how payment gateways handle reliability. Stripe famously utilizes Idempotency Keys to ensure that a network error doesn't result in a double charge. Essentially, if the server receives the same key twice, it returns the saved result of the first request rather than processing it again.
For Growth Engineers building low-code syncs, we can adapt this concept into what I call the State-Hash Guardrail Process. Instead of trusting timestamps or simple triggers, we calculate a unique signature of the data state to authorize the sync.
The Solution: The State-Hash Guardrail Process
This process acts as a governance layer that sits between your trigger and your action. It forces the automation to verify content novelty before executing a write operation.
Phase 1: The Concatenated Signature
The first step is to stop relying on the "Last Modified Time" metadata, which changes even during irrelevant updates (like system backups or unrelated field edits).
Instead, construct a "Payload Signature." In your database or via a transformation step in your automation tool (Make/n8n), concatenate the values of the specific fields you are syncing.
- Concept:
Hash(Email + Plan_Status + LTV_Score) - Implementation: Create a formula field or a variable that generates an MD5 or SHA-256 hash of these values combined.
Phase 2: The Guardrail Lookup
Before your automation writes to the destination (e.g., the CRM), it must perform a check.
- Retrieve the current Hash stored in the destination record.
- Compare it against the incoming Hash from the source.
- Filter: If
Incoming_Hash == Stored_Hash, terminate the workflow immediately.
This effectively suppresses the "Echo." When the CRM updates the Product DB, the Product DB might trigger a workflow back to the CRM. However, since the data values haven't actually changed (only the timestamp did), the Hash remains identical, and the Guardrail stops the loop.
Phase 3: The Origin Flag (Optional but Recommended)
For added safety, include a metadata field called last_updated_by.
- If the update comes from your automation, set this field to
"automation_system". - In your trigger filter, add a rule:
Only continue if last_updated_by != "automation_system".
While simple, this often fails if multiple automations are running. The Hash method is mathematically more robust.
Comparing Sync Architectures
Here is how shifting to a Hash-based approach changes the reliability profile of your growth stack.
| Metric | Timestamp Trigger (Standard) | State-Hash Guardrail |
|---|---|---|
| Loop Risk | High (Infinite Loop potential) | Near Zero (Idempotent) |
| Ops Consumption | Wasteful (Processes "ghost" updates) | Efficient (Stops at filter) |
| Data Integrity | Low (Race conditions common) | High (Content-verified) |
Why This Matters for Governance
For a Growth Engineer, "speed" is often the priority. But as your systems scale, stability becomes the bottleneck to speed. A system that loops or corrupts data requires constant manual firefighting, which kills your ability to ship new experiments.
By implementing the State-Hash Guardrail, you move from fragile, linear automations to resilient, state-aware systems. This ensures that your personalization data remains accurate and your API quotas remain healthy, regardless of how many times the triggers fire.
References
Stripe API Documentation: Idempotency Keys
Related posts
Managing API Quotas With The Throttling Governance Checklist
Stabilizing Data Pipelines With The Metadata Sidecar Process
Safeguarding Critical Workflows With The Dead Letter Queue Process
